I have collected here some useful information for our students, which complement the ones available on the excellent program website.
A recorded version of a short presentation I gave to Chalmers bachelor students in 2024 is available here.
The slides are available here.
The goal of the program
We live in a digital society, which is built on our ability to produce, transfer, store, and process digital information, i.e., bits. This program prepares you to become a digital-information engineer within the broad information and communication technology (ICT) sector, We will provide you with both the analytical skills and the applied knowledge required to imagine, design, and build the digital systems of the future.
The information and communication technology sector at a glance
So what is the ICT sector? It is good for you to know about it because, with very high probability, it will be the sector you will work in after you will leave Chalmers. It is dynamic sector that evolves at an extremely rapid pace! It isthe fastest growing sector in the Gothenburg region (Västra Götaland), where we have a world-class ecosystem consisting of large companies (Ericsson, Saab, Volvo AB, Volvo Cars, CEVT,…), as well as of small companies and start-ups. Currently, we have about 700 start ups employing around 15000 people in the region. This implies that there is a very strong demand for ICT engineers.
The information and communication technology sector in Chalmers educational offer
Let us dig a bit deeper into ICT: what are the current challenges—the ones you will most likely encounter during your professional life? Let me highlight six technologies around which most challenges, but also opportunities lie:
- Digitalization: companies want to digitalize/automatize their processes, and benefit from customers data
- Augmented reality: it may disrupt the way in which people will interact with each other, both in private and work sphere, as well as how they gather information and learn.
- Wireless communications beyond 5G: with their enhanced and ubiquitous connectivity and integrated localization and sensing, they will become integral part of many applications including smart infrastructures and autonomous vehicle.
- Internet of things: a myriad of wirelessy connected, low-cost sensors will be integrated in a network computation fabric, yielding real-time autonomous and distributed decision systems.
- Cyber security: digital transformation is prone to cyber attacks. How shall we defend it?
- Artificial intelligence: how to make AI replace humans in certain tasks? It must be secure, explainable, and fair
These technologies will shape the future we will leave in. But in which measure, it is still unclear. What will be the applications everyone will use in the next 5 years? Who will own them?
Many master programs at Chalmers prepare you for a career within ICT, by focusing on a subset of these technologies. For example, MPSYS, by highlighting the control perspective, exposes you to the first 3 challenges. If you are interesting in hardware aspects related to next generation communication infrastructure, then MPWPS is a great choice for you. MPALG takes a software perspective, and exposes you to cyber-security, AI, and digitalization challenges. Finally, if AI is what you are interested in, we have the data-science program MPDSC. MPICT is the only program, to the best of my knowledge, that exposes you to all these six technologies. Why is it good to be broad? Because you will most likely change jobs multiple times during your professional life and will move from one challenge to the next. Furthermore, innovation often happens at the boundaries between technologies. So it is good to see all of them if you are interested in disruption and innovation (for example, you plan to have your own start-ups)!
The MPICT program plan at a glance
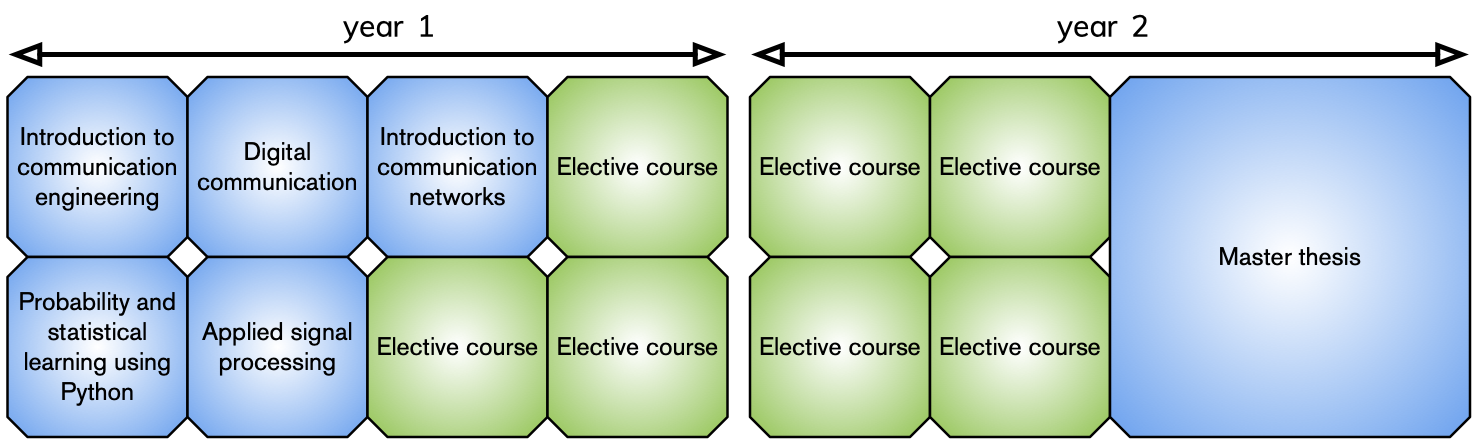
The MPICT program entails 5 compulsory courses to get an overview of the current ICT challenges and a very
broad selection of compulsory/elective, elective/courses to dig deeper into your favorite
technology.
In the figure below, we listed the 27 compulsory-elective courses that are available in
the program, divided per study period.
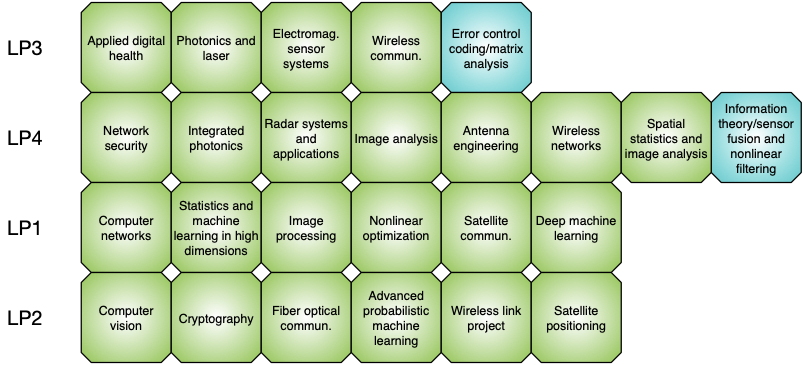
To help you with your selections, the program is organized into the following 3 tracks:
- Digital communication systems: theoretic, algorithmic, and practical aspects of digital communication systems
- Intelligent information processing: at the intersection of signal processing, sensing, computer vision, and machine intelligence
- Cognitive autonomous networks: network design and automation, security aspects
Unique features of the MPICT programs
As it is common for most programs at Chalmers, the MPICT program trains you in problem solving and critical thinking. Team work and presentation skills are honed through different dedicated moments in both compulsory and compulsory/elective courses. What’s unique is that you will be in close contact, if you wish, with a world-class academic and industrial research environment. Also, most MPICT teachers belong to one of the largest research group in Europe in the field of information and communication technologies: this implies plenty of industrial contacts, as well as many academic and industrial PhD positions available for the ones of you who are interested in doctoral studies.
]]>